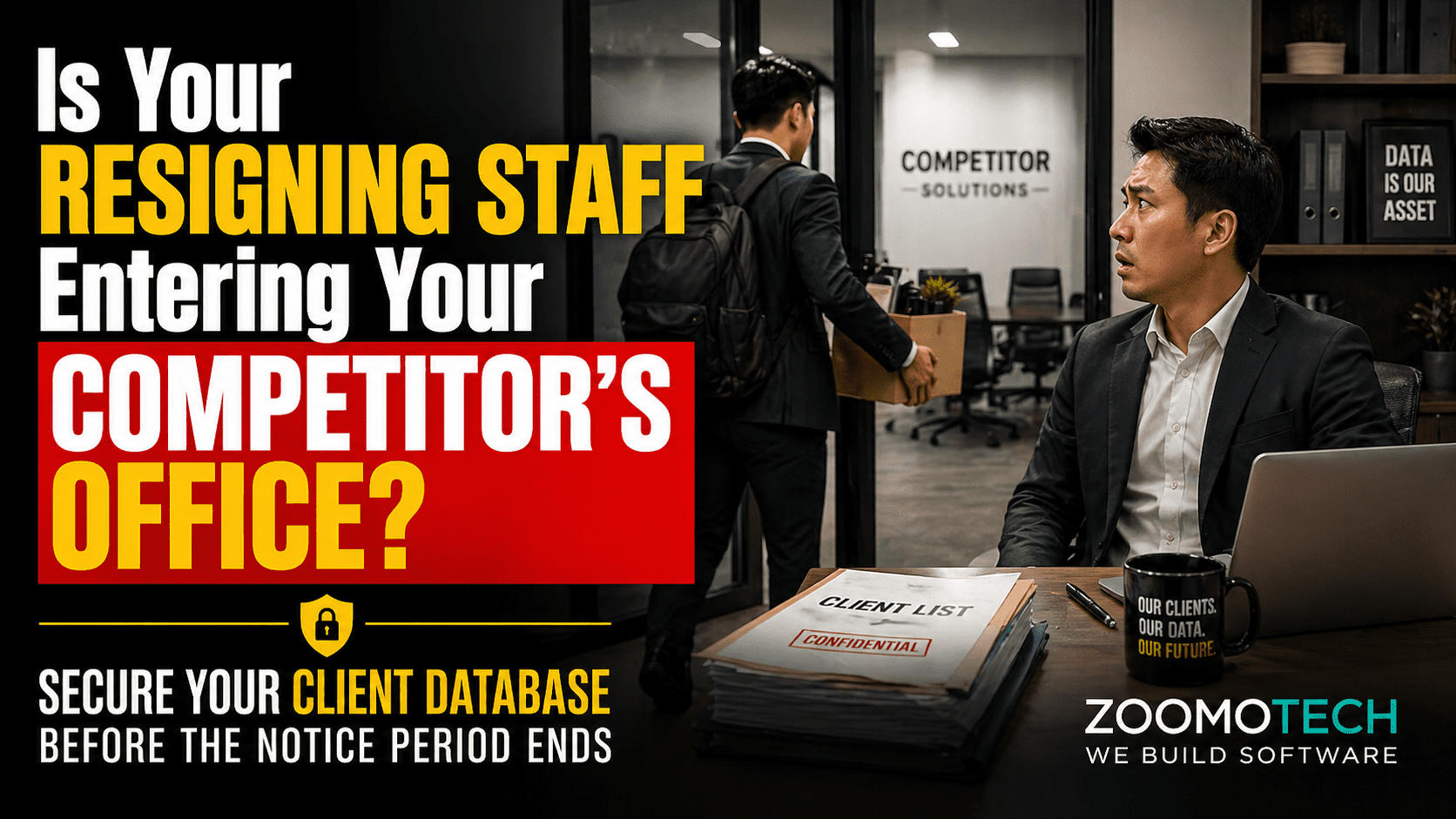
You open a resignation email, then silence follows. A week later, key customers stop replying. You realise they were dealing with your staff, not your company. Files are still there, but control is not. This is how teams quietly Steal Your Customer Database without breaking any rule.
How Manual Processes Help Staff Steal Your Customer Database?
Manual processes allow staff to Steal Your Customer Database because data access is open, untracked, and easy to copy without control:
- Excel export, USB, or email transfer
- Access not revoked after resignation
- No tracking of data activity
- Shared folders allow full download
- No structured permission system
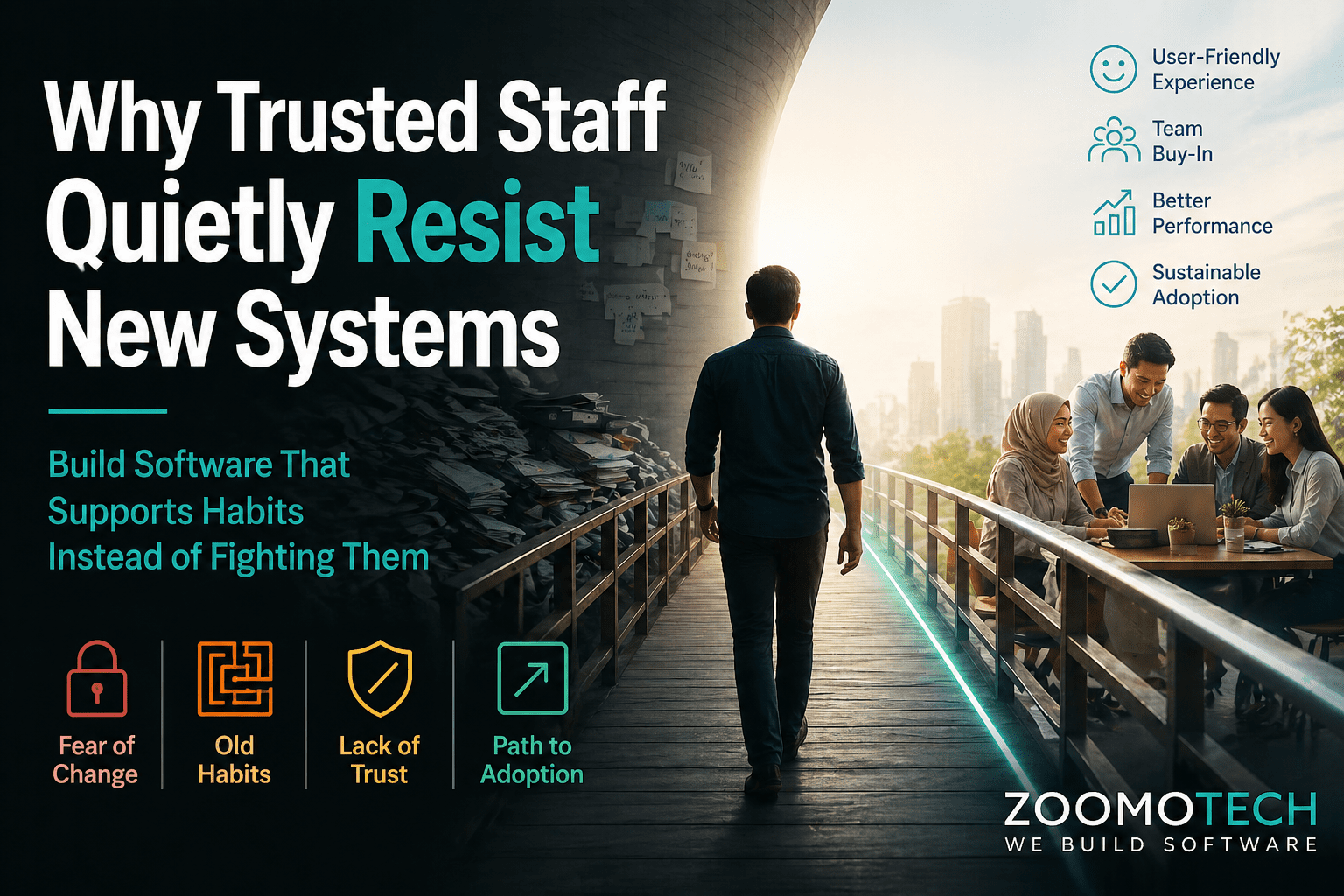
SME Growth Often Outpaces Data Protection Habits
In the early days, five staff could operate on trust alone. Customer data moved through conversations, shared files, and personal devices without issue. As the business grows, this same habit continues. Owners focus on speed and delivery, not structure. Over time, information spreads across laptops, WhatsApp, and emails without clear ownership or control.
This is not a discipline problem. It is a natural growth pattern in SMEs. When teams expand, informal handling turns into information gaps that management cannot fully monitor. The belief that “my staff is like family” worked before, but it does not scale. The next step is to understand how tools like Excel quietly make this gap worse.
Excel Spreadsheets Are the Most Leaky Data Format
Excel feels safe because it sits inside your company. But once a staff has access, control is already gone. A simple export or copy action can duplicate years of pricing, customer history, and margins in seconds. Password protection does not help once access is already given internally.
More importantly, Excel has no lifecycle control. Files do not expire, access cannot be limited by role, and copies can exist everywhere without your knowledge. Over time, multiple versions circulate across departments, similar to what we discussed in how Excel management reports hide real business problems. This is where your customer data gradually becomes portable across people and devices, without you noticing.
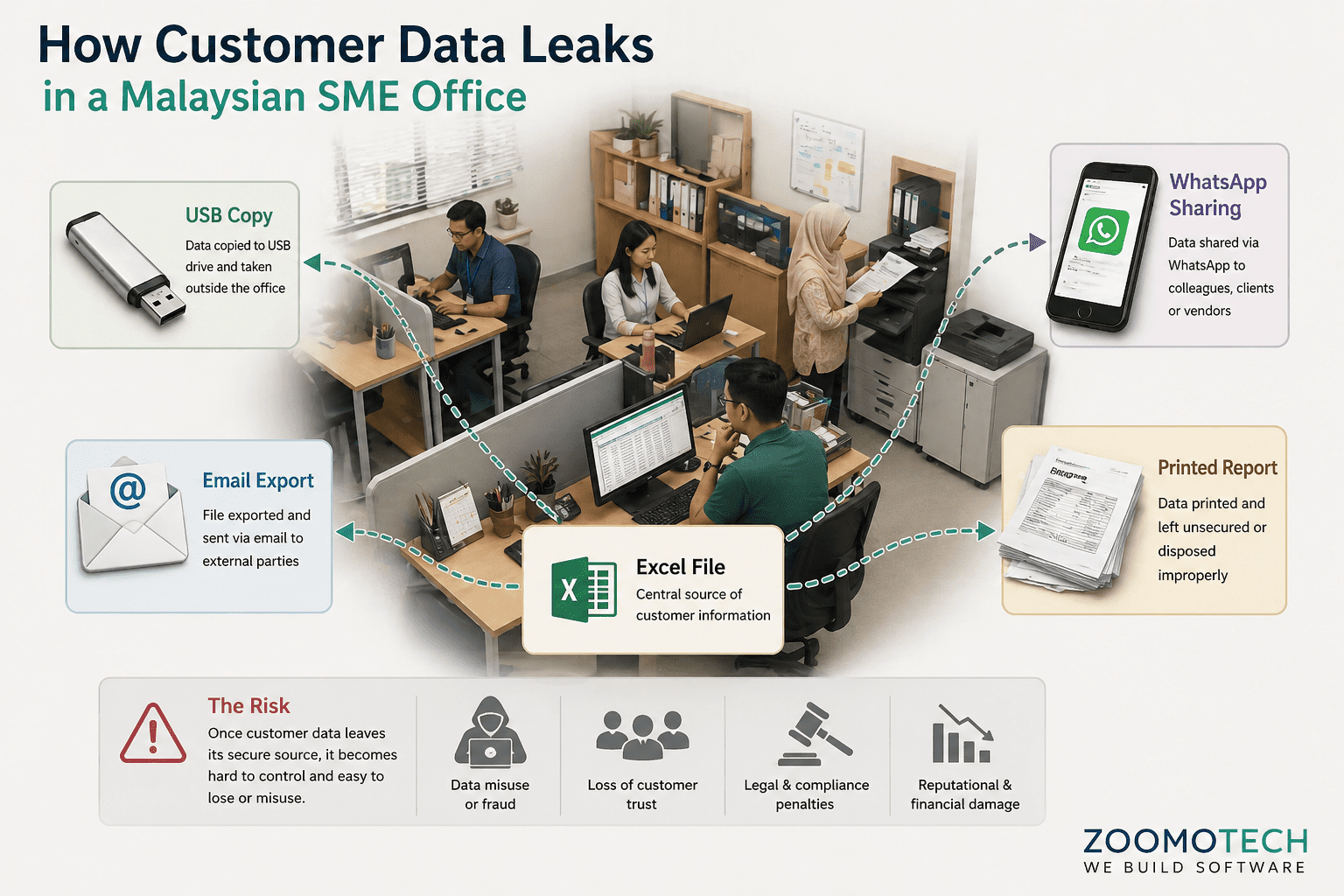
Personal WhatsApp Groups Create Company Property Risks
Many SMEs rely on WhatsApp to manage customers because it is fast and convenient. But the relationship lives inside the staff’s personal phone, not the company. Conversations about pricing, delivery, and complaints are not recorded anywhere but only inside the staff’s personal WhatsApp.
When the staff leaves, the full history goes with them. The company cannot continue the conversation properly because there is no record. Follow-ups become guesswork. Over time, the customer sees the staff as the business, not your brand. That is how customer ownership quietly shifts away from the company.
Shared Logins Make Forensic Audits Impossible
In many SMEs, systems are shared using generic accounts like “Admin” or “Sales.” This may seem practical, but it removes accountability completely. When everyone uses the same login, there is no way to trace who accessed or downloaded sensitive data.
When a problem happens, management cannot investigate. Access cannot be properly revoked because credentials are already shared. Passwords often remain unchanged for years. Without role-based control, even junior staff can access information beyond their responsibility, which often leads to the same issues discussed in why many ERP projects fail in Malaysian SMEs. Control becomes assumed instead of systematically enforced.
Mobile Access Without Governance Leaks Trade Secrets
Remote access is now normal. Staff check reports from home, access files on the go, and use cloud drives for convenience. But without control, company data moves into personal environments without restriction.
Files can sync automatically to personal accounts. Screenshots can be taken and shared. There is no reliable way to remove company data once it leaves the device. Casual sharing between colleagues through non-work apps becomes common. Over time, sensitive information spreads beyond the company boundary without clear awareness.
Why Trade Secret Leakage Happens During Notice Periods
The notice period is often treated as a transition phase, but it is also the highest risk window. Staff still have full access, but their intention may already change. With weeks or months available, data can be collected gradually without raising attention.
At the same time, management focuses on replacement and handover. Monitoring becomes secondary. Files may be downloaded for “reference,” and customers may be contacted quietly. By the time the staff leaves, the exposure has already happened. This is where the real business impact begins.
Losing Your Client List Directly Impacts Future Revenue
What starts as a staff issue quickly becomes a business problem. When your customer list moves out, competitors gain ready access without spending on marketing. They know your pricing patterns and margins, making undercutting easier. Existing customers may feel uncertain when approached by a familiar face from another company.
At management level, this affects long-term positioning. Legal action is slow and often costs more than the data itself, especially when obligations under Malaysia Personal Data Protection Act (PDPA) are not clearly enforced internally. More importantly, your competitive edge, built over years of relationships and pricing experience, begins to weaken, similar to what we mentioned in how manual business operations increase hidden operational cost over time. This is where protecting business trade secrets becomes a management-level structural decision, not just a HR concern.
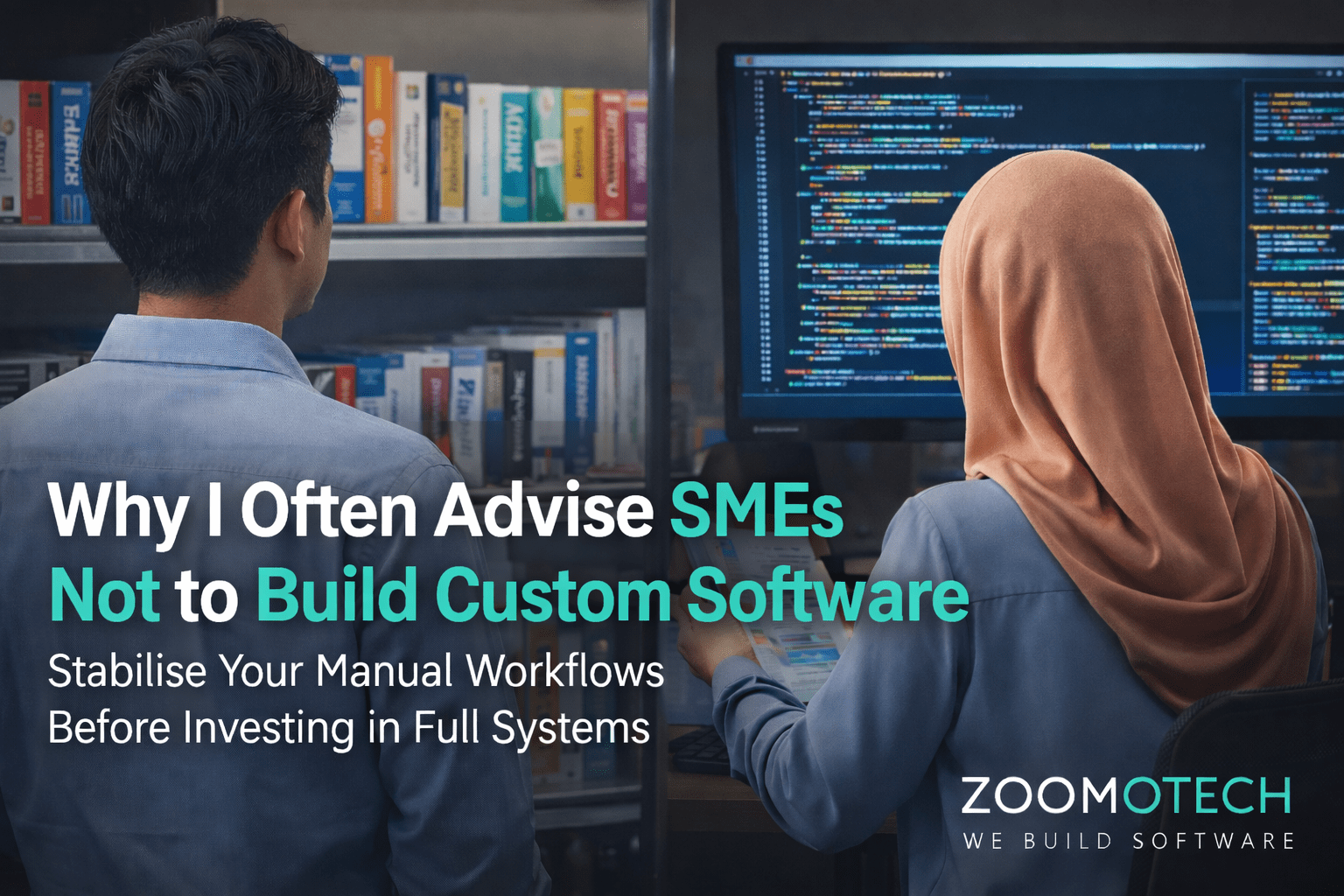
Protect Business Trade Secrets via Digital Ownership
Protecting data does not mean removing trust. It means adding structure around it. As businesses grow, customer data should be treated as a balance sheet asset, not a shared file. A phased approach allows control to build gradually with clarity before commitment, so risk is reduced without disrupting daily operations.
Securing Your Legacy Starts With One Secure Workflow
Manual systems were built for convenience, not for long-term control. That is why they cannot prevent situations where staff quietly Steal Your Customer Database. A custom made structured system creates a clear digital boundary, where access, ownership, and activity are clearly defined. This is not about control for restriction, but control for continuity. When data stays with the company, growth becomes more stable, and decisions become more reliable over time.
If you are unsure where your current exposure is, this may be a good time to review it calmly. You can reach me out via WhatsApp or Email for a simple discussion on your existing data flow. No pressure, no commitment, just a clearer view of where you stand today.
—
Ning
Founder, Zoomo Tech